As a blogger, you have followers because of the unique value that you create. To build a strong community, you need to build trust by consistently creating reliable content. To do this, it takes years of regular publishing before your blog builds enough credibility to be a figure of authority on the internet.
Unfortunately, many bad actors see this as an opportunity to take control over your profile for nefarious means. Through the trust you have cultivated, these bad actors can trick your followers into clicking phishing emails, participating in scams, sending money to impersonators, and so on.
To protect your followers and the brand you’ve worked so hard to build, here are some ways to protect yourself.
- How bloggers can protect themselves outside of social media
- Security and privacy settings bloggers should know about on social media
- Protect yourself online as blogger
How bloggers can protect themselves outside of social media
Before you use social media, you should invest in ways to secure your personal information. As a blogger, you will also have to deal with other security concerns outside social media to stay safe from hackers, imposters, or people looking to take advantage of your following.
- Website privacy registration
- Password management
- Antivirus programs
Website privacy registration
ICANN requires that personal information on website owners be always available to the public, which means that anyone can search for your full name, address, and other records by checking the public database on WHOIS.
To avoid revealing your personal data, you can invest in additional domain privacy features from your domain registration company. With this, your personal information will not be available for public viewing. Instead, your domain provider will be listed instead.
Password management
To grow a blog’s following, many bloggers also have to promote their content on dozens of social media platforms all at once. With this, it’s common to make a single password for every account.
In the Password Usage Study, cybersecurity firm HYPR revealed that 72% of individuals reused passwords. Unfortunately, this isn’t recommended for a variety of reasons because once this password is compromised, hackers can access all your accounts.
For this reason, it’s important to not only create strong passwords, but also have multiple passwords across platforms. Using password management apps, bloggers can be sure that all their passwords are strong, difficult to guess, and safe.
Antivirus programs
Because bloggers often work remotely, it is highly likely that you will have to connect to Wi-Fi signals that are not always safe. In addition, bloggers also coordinate hundreds of potential partners at a time. For this reason, you are at risk of accidentally clicking phishing emails or scam text messages.
With this, it’s best to invest in real-time antivirus for Mac to keep you and your personal data safe from harm. Whether it’s malware, spyware, or ransomware, antivirus protection is well worth the investment for both your safety and privacy.
After having a good foundation of data privacy and security practices, you can proceed to modify your social media settings to protect your identity, intellectual property, and overall internet safety.
Security and privacy settings bloggers should know about on social media

One of the most common ways to promote your blog is through Facebook. Here are some ways to help keep your Facebook account safe:
- Enable Two-Factor Authentication (2FA) on Facebook
- Get alerts about unrecognized logins on Facebook
- Select trusted friends for account lockout on Facebook
Enable two-factor (2FA) on Facebook
From your Facebook profile on the browser, click the dropdown arrow in the upper-right corner of the screen. Next, select Settings & Privacy > Settings > Security and Login.
Under Two-factor authentication, click Edit next to use two-factor authentication. Afterward, select which 2FA method suits you the most. On Facebook, there are three ways that you can get additional account verification-authentication app, security key, and SMS message.
Get alerts about unrecognized logins on Facebook
As a blogger, you may need to log in from multiple devices at a time. However, it’s good to enable notifications for when a login doesn’t seem to match your usual patterns.
To get alerts about unusual logins using your Facebook account, click the dropdown arrow in the upper-right corner of the screen.

Next, select Settings & Privacy > Settings > Security and Login. Under Setting Up Extra Security, click Edit next to Get alerts about unrecognized logins.

Then, select if you would like notifications inside the Facebook app, Messenger, or email address. Lastly, select Save changes to confirm your preferences.
Select trusted friends for account lockout on Facebook
For bloggers, losing access to their Facebook account can mean a loss of opportunities. If a hacker was able to get a hold of your account, Facebook may lock it for your safety. Because of this, you should consider setting up trusted contacts who can help you regain control of it quickly.
To select friends that Facebook can contact if you are locked out of your account, go to your Facebook account and click the dropdown arrow in the upper-right corner of the screen. Then, select Settings & Privacy > Settings > Security and Login.

Under Setting Up Extra Security, click Edit next to Choose 3 to 5 friends to contact if you get locked out. Then, click Choose friends > Choose Trusted Contacts.

Next, type the name of your preferred contacts and press confirm.

With many bloggers using their platform to secure more clients, it’s becoming increasingly common for bloggers to be active on LinkedIn. However, LinkedIn has a long history of data breaches that make it difficult to trust when it comes to your personal data. Here are all the important privacy settings bloggers should know to protect our privacy on LinkedIn:
- Manage cookie preferences on LinkedIn
- Disable advertising preferences on LinkedIn
- Hide data collected on LinkedIn
- Stop sharing data with third-party advertisers on LinkedIn
Manage cookie preferences on LinkedIn
Cookies are used by LinkedIn to follow your activity outside their website for advertising, analytics and research, and to improve some of our features and services.
To prevent LinkedIn for putting cookies on your browser, click your profile photo in the top-left corner of the screen.

Next, select Settings & Privacy > Advertising Data. Under Manage cookie preferences, click Change and toggle off the button next to Cookies.
Disable advertising preferences on LinkedIn
To disable your advertising preferences on LinkedIn, there are two critical features to disable—personalizing data for personalizing ads and interest categories. Here’s how to do both.

First, click your profile photo in the top-left corner of the screen. Next, select Settings & Privacy > Advertising Data. Under Advertising Preferences, go to Profile data for personalizing ads. Then, click Change and toggle off the button.
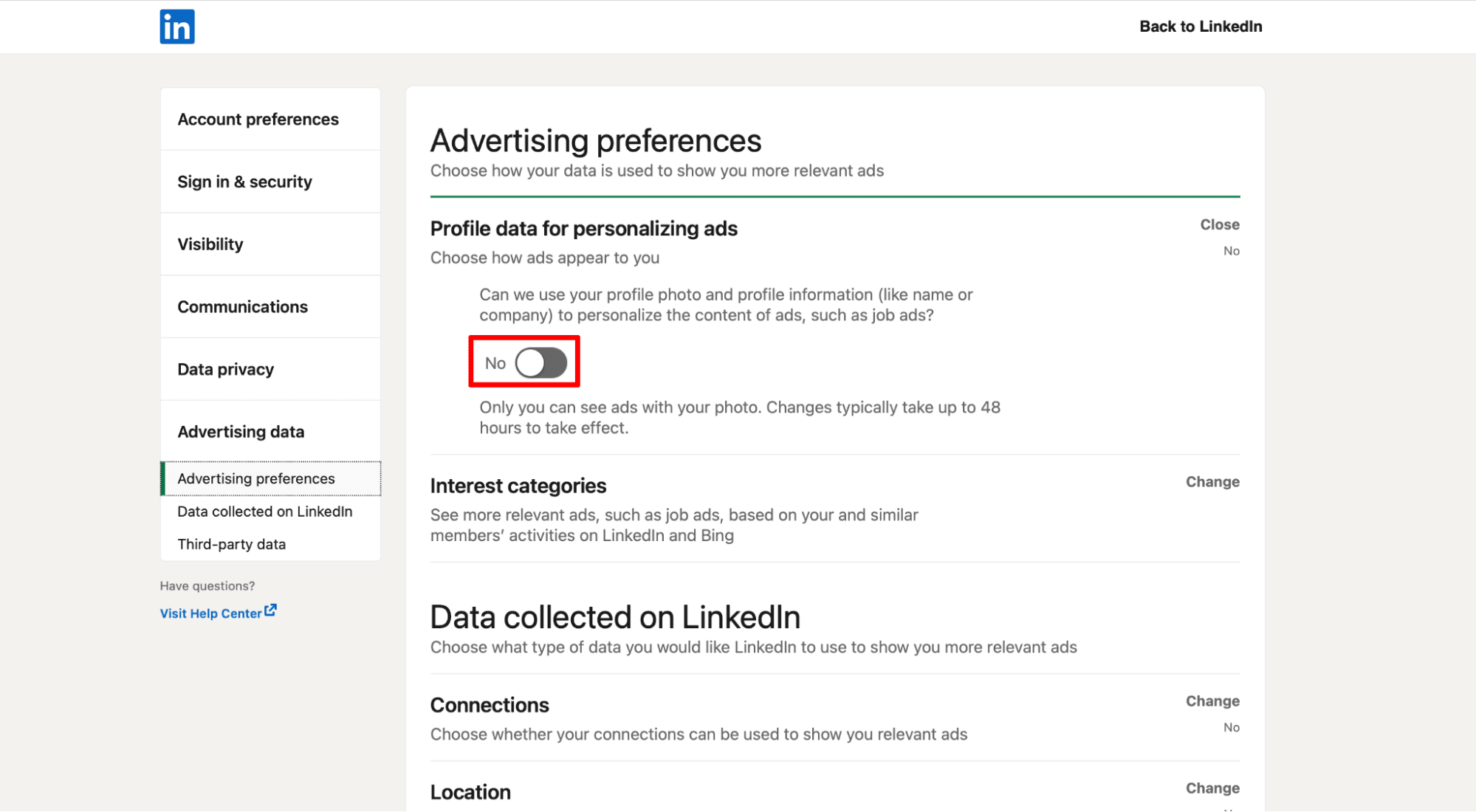
Second, you can proceed in disabling interest categories by clicking Change. Next, toggle off the button next to Interest categories.

Hide data collected on LinkedIn
Once you disable advertising preferences, it is best to prevent LinkedIn from using your data to serve you relevant ads inside the platform. To accomplish this, click your profile photo and go to Settings & Privacy > Advertising Data.
Under Data collected on LinkedIn, you can click Change and toggle off the button next to Connections, Location, Demographics, Companies you follow, and groups.
Next, click Change to the right of Education. Then, uncheck the fields next to Schools, Field of Study, Degrees, Skills, and Last graduation year.

Click Change to the right of Job information and uncheck the box next to Current job and Past jobs.
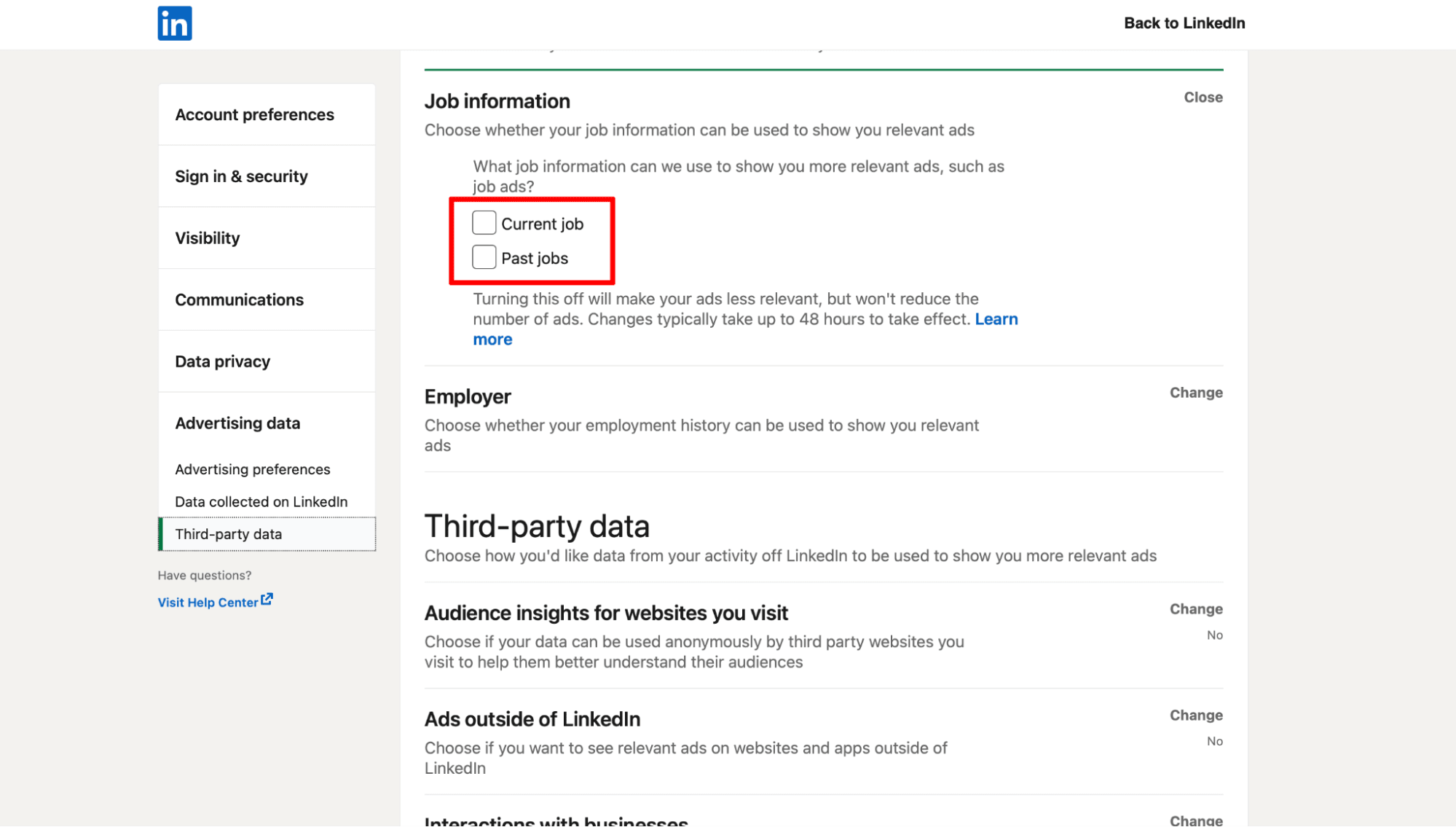
Lastly, click Change to the right of Employer and deselect the box next to Current company and past company.
Stop sharing data with third-party advertisers on LinkedIn
After disabling advertising preferences and hiding your LinkedIn data, the next step is to stop sharing your data with third-party advertisers. Based on information from your LinkedIn activity, this is data that can be used by third-party advertisers to give you personalized ads outside the platform.

To make sure third-party advertisers don’t get a hand of your personal information, go to your profile photo> Settings & Privacy > Advertising Data and scroll down to the Third-party data section.
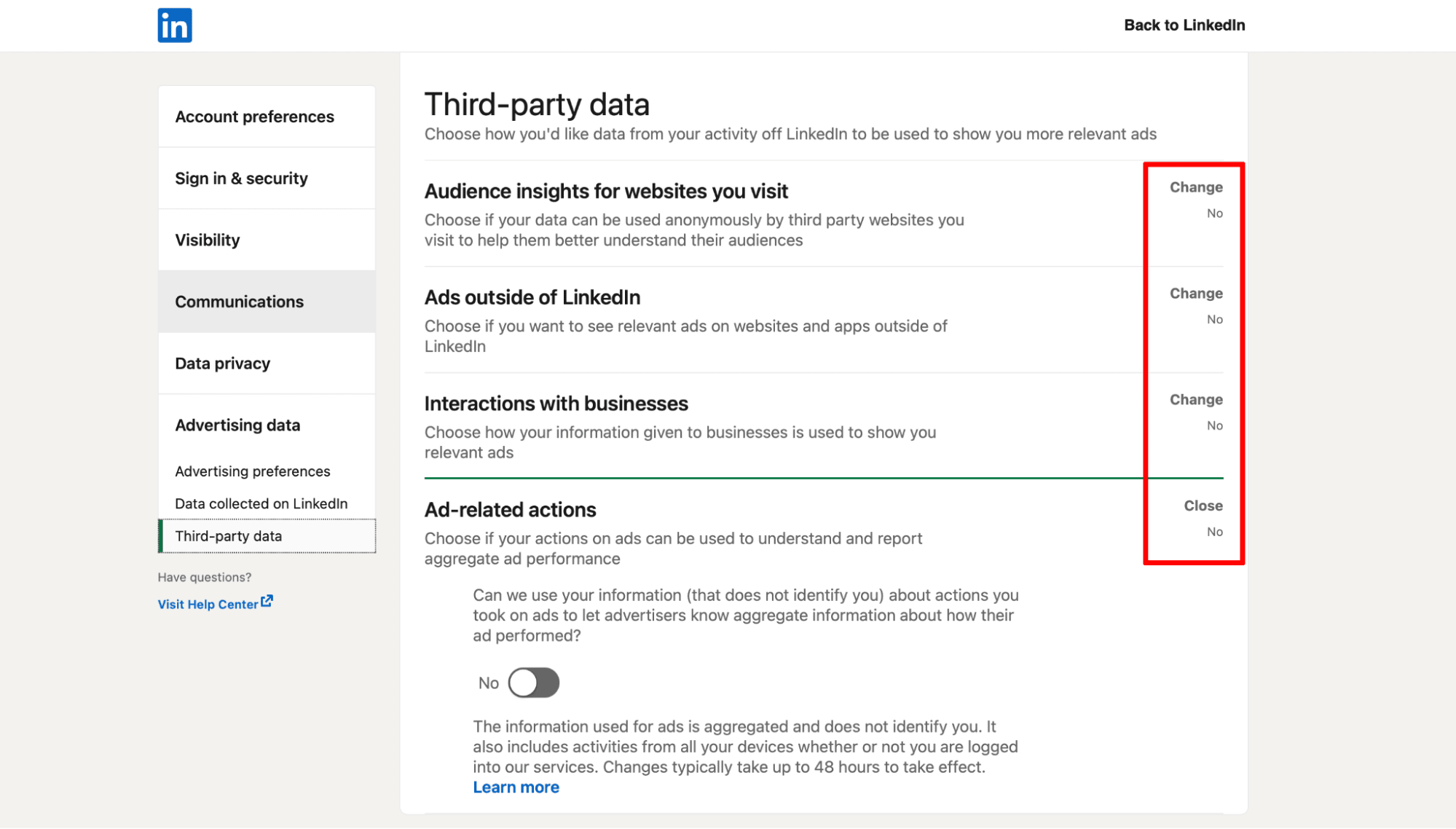
Then, click Change and toggle off every button next to Audience insights for websites you visit, ads outside of LinkedIn, Interactions with businesses, and Ad-related actions.
To reach potential readers, bloggers often remain public profiles on Instagram. However, there are still several settings that you can have to secure your account from people who want to take advantage of your following for scams. Here are the Instagram settings you need as a blogger:
- Activate Two-Factor Authentication on Instagram
- Limit Unwanted Interactions on Instagram
Activate Two-Factor Authentication (2FA) on Instagram
With Two-Factor Authentication, you can be sure that you’ll know right away if someone is trying to access your Instagram account. To do this, go to Settings > Security > Two-Factor Authentication.

From there, select the best way for you to get your log-in codes. As of now, Instagram lets you choose between WhatsApp, Authentication App, text message, login requests, or backup codes to receive log in codes.

Limit Unwanted Interactions on Instagram
As bloggers, keeping an engaged community is key to staying relevant. Unfortunately, Instagram is filled with bots, scammers, and harassers. To make sure that your followers don’t have to sift through a mountain of comments from these questionable profiles, it is best to limit unwanted interactions on Instagram.

To limit fake profiles, toxic people, and bots from taking over your comment section, go to Settings > Privacy > Limits and tap Continue. Next, choose whether to limit accounts that aren’t following you or recent followers by toggling off the buttons. Lastly, set how long to limit these users from 1 day to 4 weeks.
YouTube
In some cases, bloggers are also vloggers who use YouTube to share their content or experiences. However, not all bloggers want to give their followers access to their personal viewing habits. Knowing this, here are some ways for you to keep your YouTube channel private as a blogger:
- Keep your playlists private on YouTube
- Hide your subscriptions on YouTube
Keep your playlists private on YouTube
Even if you’re a blogger, not all your followers need to know about your personal playlists on YouTube. If you prefer to keep your playlists private, go to YouTube and click your account profile photo.

Next, go to Settings > Privacy. Then, toggle off the button next to Keep all my saved playlists private.

Hide your subscriptions on YouTube
Aside from being content creators, bloggers are also content consumers. However, it doesn’t always look good for your personal brand to subscribe to a certain channel.
To keep your subscriptions away from public view, go to Settings > Privacy. Then, toggle off the button next to Keep all my subscriptions private.

Using Pinterest, many bloggers grow their following by sharing pins of their latest posts. However, Pinterest also collects countless personal data about bloggers in return. To prevent Pinterest from breaching your privacy, here are the critical Pinterest privacy settings that every blogger should know about:
- Claim your owned channels on Pinterest
- Disable ad personalization on Pinterest
Claim your owned channels on Pinterest
As a blogger, you want to be able to get credit for the content you created which are shared on Pinterest. To avoid other people pretending to be you, you must first claim your website on Pinterest.

To do this, click the Arrow Down next to your Logo and Settings > Claim.

Next, click Claim next to your website name. From there, you can add an HTML tag to your website code, upload an HTML file to your website’s root directory, or add a TXT record to your domain host.

If you have an Etsy shop, you can also claim it by clicking Claim next to Etsy. After, you will be redirected towards your Etsy account where you can follow the instructions.

Lastly, you can also claim your YouTube channel. To complete this, click Claim next to YouTube and follow the instructions on the screen to proceed.

Disable ad personalization on Pinterest
As a blogger, it is best to allow anyone to mention you and disable search privacy. However, there is no need for you to enable your ad personalization.
To disable this, go to click the Arrow Down next to your Logo and Privacy and Data. Under Personalization, uncheck all the options and click Save.

Protect yourself online as blogger
On the journey of becoming a top blogger, there are many moving parts. Aside from choosing the right imagery for your branding, creating content, designing promotional materials, and making sure people see your work, you also have to make sure that you don’t put yourself and those close to you in danger. As your blog grows, so do the risks associated with your position as a public figure.
For this reason, building a foundation of good privacy and security is essential to a safe blogging experience. By making sure everything from your legal documents, device, internet connection, to social media settings are safe, you can have a long, lucrative career as a blogger with fewer problems.